Using privacy-preserving ZKP credentials on the MATTR Platform
MATTR is proud to announce we’ve added support for privacy-preserving verifiable credentials on our platform using BBS+ signatures. Using a technique to implement selective disclosure, we’ve added the ability to generate credentials that support zero knowledge proofs without revealing any unnecessary information about the end-user, or placing any added burden on issuers, in the process. Since we first introduced and open-sourced JSON-LD BBS+ Signatures at IIW30 in April of this year, we’ve received lots of engagement, feedback and contributions from the broader technical community to further develop the implementations and specifications we presented. You can read more about our approach to privacy-preserving verifiable credentials on our introductory blog post.
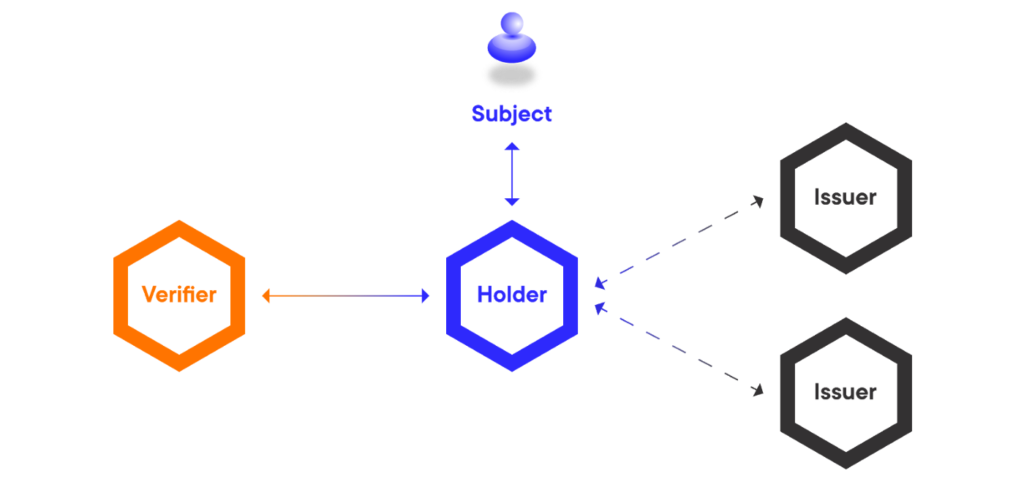
One of the benefits of using the BBS+ cryptographic scheme to sign credentials is the ability to derive a zero knowledge proof from the signature, where the party generating the proof can choose to partially disclose statements from the original message. When enabled, this feature allows issuers to create a credential that effectively enforces minimal data disclosure using the MATTR Platform and a compliant digital wallet.
 Issuers can create ZKP-enabled credentials that allow the user to selectively disclose data
Issuers can create ZKP-enabled credentials that allow the user to selectively disclose data
To support this functionality, we generate the keys required to support these signatures and create a Decentralized Identifier (DID) with the keys referenced in the DID Document. BBS+ signatures require what’s called a pairing-friendly curve, we use BLS12–381. This DID can be referenced in credentials to establish the issuer of the data, a common practice to allow a verifier or relying party to trace the root of trust in a credential.
To issue a ZKP-enabled credential, simply use our API endpoint to create a new DID Key with type set to BLS 12–381. Then, create a Verifiable Credential (VC) using your new DID Key as the issuer DID. Our platform will automatically detect this capability is available in your DID and create a ZKP-enabled BBS+ credential for you. You can use the platform this way to create a privacy-enabled credential, or you can create a regular credential by providing a DID with a different key type — you have the option.
On the user side, you can hold ZKP-enabled credentials in your wallet alongside all of your other credentials. We’ve designed this process in a way that minimizes friction to the user. In future updates, our Mobile Wallet App will be able to detect if BBS+ signatures are being used in a credential. When you get a request to verify some information contained in one of these privacy-enabled credentials, it will derive a new presentation that selectively discloses the required info using a zero-knowledge proof. The platform will then allow verification of the proof using the same interface as any other type of presentation.
Our integrated approach treats zero-knowledge proofs as an extension of VCs, rather than an entirely new framework with a separate set of dependencies. We have built BBS+ Signatures and privacy-enabled credentials into our platform for anybody to experiment with, in what we think is a significant milestone for standards-based credential solutions on the market today.
As a technology, BBS+ digital signatures can be used to sign more than just verifiable credentials. Combining these technologies is quite effective, though they can also be treated as modular or separate components. We’ve open-sourced software for creating and verifying BBS+ signatures in browser environments as well as node.js, and we’ve also published a library for generating BLS 12–381 keypairs for signing and verifying BBS+ Signatures.
By leveraging pairing-friendly elliptic-curve cryptography in the context of Linked Data Proofs, our approach provides an unprecedented way to perform zero-knowledge proofs using the semantics of JSON-LD. This allows credential issuers to tap into vast data vocabularies that exist on the web today, such as schema.org and Google Knowledge Graph, making user data more context-rich without sacrificing security and privacy of the user in the process. Not only is this approach more interoperable with existing implementations of the VC data model and semantic web technologies, it also doesn’t rely on any external dependencies to operate (like a distributed ledger), meaning it’s far more efficient than other approaches based on CL-signatures and zk-SNARKs. We’ve open-sourced our LD-Proofs suite for VCs including performance benchmarks so you can check it out yourself.
We’re excited to finally make these powerful privacy features easily accessible for everyone, and we can’t wait to see what you build with it. To get started, sign up now on our website and follow our tutorials on MATTR Learn to start creating ZKP-enabled verifiable credentials on the MATTR Platform.
Additional Links
Open-source:
- Node JS BBS+ Signatures — BBS+ signatures implementation for node.js environments
- WASM JS BBS+ Signatures — BBS+ signatures implementation for browser & node.js environments
- BLS 12–381 Key Pair JS — crypto keys for signing/verifying BBS+ signatures
- BBS+ JSON-LD Signatures JS — uses BBS+ signatures & BLS 12–381 keypair in a Linked Data Proofs suite (for use in VC implementations)
Specifications:
- BBS+ Signatures Spec — definition of BBS+ signatures scheme