Australia is entering a more consequential phase of digital identity development.
The country now has many of the foundations required for a modern digital trust environment: a legislated Digital ID regime, mature identity verification services, national proofing guidance, assurance models, credential activity, wallet initiatives, and growing policy momentum toward more portable and privacy-preserving ways for people to prove who they are.
This is meaningful progress.
But it is important to be precise about the current state of the system. Australia does not yet have a single, fully joined-up operating model for how Digital ID, identity verification, proofing, credentials, wallets, assurance, and relying party obligations should work together across the economy.
The parts are increasingly visible. The connective tissue is still forming.
That is not a criticism of the work underway. It is the reality of building serious trust infrastructure across government, regulated industries, state and territory systems, private-sector onboarding, fraud controls, privacy obligations, and sector-specific compliance regimes.
These systems should take time to mature. They need to.
The more important question for organisations is what to do while that maturation is happening. Because waiting until every framework, rule, liability position, and reliance pathway is fully settled may feel prudent. In practice, it may become the reason organisations fall behind.
Australia has strong layers of trust infrastructure
Australia’s digital identity environment is not starting from scratch.
The Australian Government Digital ID System, or AGDIS, provides a legislated trust framework for digital identity. It is designed around accredited participation, assurance levels, privacy protections, technical standards, liability settings, and rules for how identity information can be shared and relied upon within a governed environment.
The Identity Verification Services, or IVS, ecosystem provides another layer of national capability. Services such as the Document Verification Service, Face Verification Service, and the National Driver Licence Facial Recognition Solution support organisations to verify identity information against authoritative records. These services are already deeply embedded in onboarding, compliance, fraud reduction, and remote identity checks.
Alongside this, verifiable credentials and digital wallets are introducing a different model again. Rather than requiring an organisation to repeatedly collect documents or query source systems, a trusted issuer can issue a credential to an individual, who can then hold it and present it later. A relying party can verify that credential and make a decision about whether to accept it.
Each of these layers matters. But they do not all do the same job.
The core blocker is not technology. It is reliance.
Much of the technology needed to issue, hold, present, and verify digital credentials already exists.
Organisations can already verify documents through DVS. They can use biometric matching through services such as FVS. They can implement credential issuance and verification flows. They can design wallet-based experiences. They can test selective disclosure, remote verification, in-person presentation, and reusable identity journeys.
The harder question comes after the technology works:
Can I rely on this, in this context, for this purpose?
A bank may be interested in accepting a digital credential during onboarding, but still need to know whether that credential satisfies its anti-money laundering and counter-terrorism financing obligations.
A telecommunications provider may be able to verify a digital credential technically, but still need confidence that accepting it meets its identity verification obligations and fraud controls.
A university may want to issue or accept verified student, qualification, or eligibility credentials, but still need to understand how those credentials will be recognised by employers, licensing bodies, government agencies, or other education providers.
A state government may issue a mobile driver licence, but relying organisations still need to decide what role that credential plays in their own risk, compliance, and service delivery environments.
In each case, the issue is not whether digital trust can be created. It is whether that trust is recognised, sufficient, and defensible in the receiving context.
That is why adoption is uneven.
A credential can be technically valid and still not be operationally decisive. A verification event can be high confidence and still not produce a portable trust outcome. A person may have proved who they are in one setting and still be asked to prove it again somewhere else.
This is the gap Australia is now working through.
Verification is strong, but not reusable by default
Australia’s verification infrastructure is a major strength.
The Document Verification Service allows organisations to check identity document details against authoritative records. The Face Verification Service helps establish that the person presenting is linked to the relevant record. The National Driver Licence Facial Recognition Solution supports biometric verification capability across driver licence records.
These services reduce fraud, support remote onboarding, and give organisations confidence that identity information matches source records.
But they produce verification events.
They do not, by themselves, produce a reusable identity object that another organisation can automatically rely on later.
Consider a customer opening an account with a financial services provider. They submit identity documents. The provider checks those details through DVS and may perform additional biometric checks. The provider reaches a decision: this customer has satisfied the identity requirements for this account opening process.
That result is valuable. But it usually stays inside that organisation.
If the same person later signs up with a telco, applies for a government service, rents a property, enrols in a university course, or proves eligibility for a concession, they may be asked to go through a similar process again.
The same person.
The same underlying evidence.
Often the same national verification infrastructure.
But a different relying organisation, a different compliance context, and a different local decision.
This is why stronger verification does not automatically produce reuse. The system is good at helping organisations answer, “Can I trust this person for this transaction?” It is less mature at answering, “Can this trust outcome move safely into another transaction without being recreated from scratch?”
That is the transition now underway: from validation to continuity.
Proofing remains the front door
Proofing is where identity becomes an accepted outcome.
It is the process through which documents, records, personal attributes, biometric checks, and other evidence are assessed against a required assurance level. In higher-assurance settings, proofing may require multiple identity documents, checks against authoritative sources, facial matching, or additional controls.
That makes sense. Higher-risk transactions require higher confidence.
But proofing is also where the practical friction of digital identity becomes visible.
Someone may have a maiden name on one document, a shortened name on another, and a hyphenated surname in a different system. Their address history may not line up neatly across databases. Their driver licence image may be old. Their document may be worn. Their phone camera may struggle with glare. Their living circumstances may mean they do not have the expected combination of documents.
These are not edge cases. They are normal realities of identity infrastructure operating at population scale.
The challenge is that proofing often depends on several things going right at once. The record needs to match. The document needs to capture properly. The face match needs to work. The person needs to understand the flow. The system needs to handle exceptions well.
When it works, the experience can be smooth. When it fails, the person may be diverted to manual review, asked to try again, pushed into a branch or service centre, or required to produce alternative evidence.
That may be manageable once.
It becomes much more significant if similar proofing journeys are repeated across banking, telecommunications, government services, healthcare, employment, education, and insurance.
This is one of the most important structural blockers to adoption. Strong proofing is necessary, but a mature digital identity system should not require strong proofing to be repeated unnecessarily. The goal is not to lower assurance. The goal is to establish assurance well, then make the resulting trust more portable.
Credentials are promising, but relying parties need to know what they mean
Verifiable credentials change where trust sits in the transaction.
In the current validation-heavy model, a relying organisation often collects evidence and checks it directly or indirectly against source systems. Trust is reconstructed at the point of need.
In a credential model, the issuer performs the assurance-heavy work earlier. It verifies the relevant information, issues a credential, and the individual can later present that credential to another organisation. The relying party can verify the credential’s integrity, issuer, status, and claims.
This has obvious benefits.
A person may not need to repeatedly upload identity documents. A relying party may not need to collect more information than necessary. A credential could prove that someone is over 18 without revealing their full date of birth. It could prove that someone holds a valid licence without exposing unrelated document details. It could prove eligibility, status, qualification, membership, employment, or entitlement with less friction and less data sharing.
But the credential only changes the operating model if it is accepted in place of the old process.
A mobile driver licence is a useful example. It may be government-issued, familiar to users, and technically capable of being verified. But a relying party still has to decide what it can use it for.
Is it sufficient for age verification? Is it sufficient for onboarding? Is it sufficient for regulated identity verification? Does the organisation need to check it live? Does it need to retain evidence? Does it need additional proofing? Does accepting it change liability?
The credential itself does not answer all of those questions. The surrounding framework, regulation, assurance model, and relying party policy need to answer them too.
This is why Australia is currently moving faster on credential capability than on credential reliance.
Issuance is becoming more practical. Acceptance is becoming more familiar. But routine, cross-sector reliance is still maturing.
AGDIS is essential, but it is not the entire ecosystem
AGDIS is a major step forward because it creates a governed environment for Digital ID.
It defines roles, rules, accreditation, assurance, privacy protections, and operating conditions. Within its boundaries, trust becomes more structured and more accountable.
But AGDIS is not the entire identity ecosystem.
Australia also has state and territory credentials, sector-specific evidence requirements, IVS-based verification models, private-sector onboarding systems, and emerging wallet and credential models that may intersect with AGDIS without being identical to it.
That means organisations need to understand the boundaries.
Progress inside AGDIS does not automatically settle how every digital credential will be treated across every sector. A credential may be used inside an AGDIS context, outside it, adjacent to it, or as part of a broader trust ecosystem.
A relying party may need to understand the difference between relying on a Digital ID transaction within an accredited framework, verifying a document or biometric match through IVS, accepting a government-issued mobile credential, verifying a verifiable credential from a trusted issuer, or combining credential evidence with additional internal controls.
These are related, but they are not interchangeable.
This is where organisations need grounded expertise. The practical question is rarely, “Should we use digital identity?” It is more often:
Which trust pathway applies to this use case, what assurance does it provide, and what would we need in order to rely on it?
What is likely to come next
The next phase of Australia’s digital identity development will be less about proving that the technology works and more about making reliance repeatable.
Several shifts are likely to define that phase.
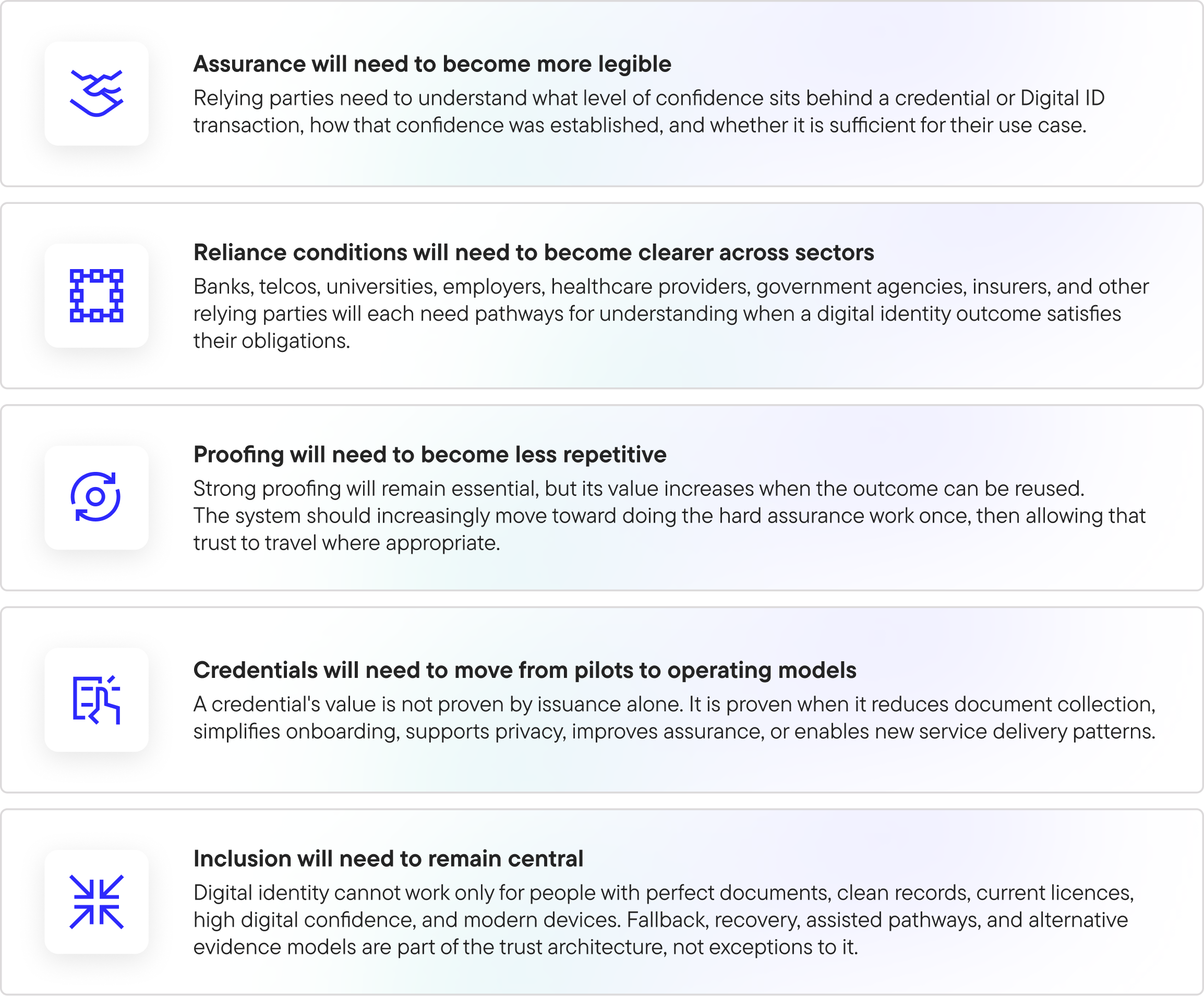
These changes will not arrive in one moment. They will emerge through framework maturity, policy clarification, sector adoption, standards implementation, and practical deployments.
That is exactly why organisations should start learning now.
What this means for organisations
For a large organisation, preparing for digital identity is not simply a matter of waiting for a compliance memo and then procuring a platform.
It requires operational learning.
A bank may need to test how a credential-based onboarding flow interacts with existing know-your-customer controls, fraud systems, document retention policies, and customer support pathways.
A telco may need to evaluate whether a digital credential can reduce identity fraud while limiting unnecessary collection of sensitive documents.
A university may need to explore how student credentials, qualifications, enrolment status, or eligibility claims could be issued and verified across employers, government programs, and other education providers.
A government agency may need to understand how a wallet-based model changes service access, eligibility proof, concession management, licensing, permits, or citizen-facing claims.
An employer may need to test how verified qualifications, right-to-work status, professional licences, or training credentials can simplify hiring and compliance.
None of this can be solved in theory alone.
Organisations need to test which credentials matter, what data needs to be disclosed, how verification fits existing systems, what user experience is acceptable, what risk teams require, what legal teams need to understand, and where older processes can actually be removed rather than duplicated.
That learning takes time.
Readiness is the work to do now
MATTR’s view is that Australia’s digital identity framework is moving in a clear direction, even though many of the operational details are still maturing.
That is precisely the moment when organisations should begin preparing.
Not by assuming every question has been answered. And not by betting on a single future state before the ecosystem is ready. But by building practical understanding now through proof-of-concept work, targeted use case exploration, internal education, architecture planning, and early implementation patterns that can evolve as frameworks mature.
MATTR provides digital trust infrastructure for issuing, holding, presenting, and verifying digital credentials across remote and in-person interactions. We work with organisations that need to understand how credential models operate in real environments: how they integrate with onboarding, compliance, fraud management, service delivery, customer experience, privacy, and assurance requirements.
This is not only a technology transition. It is an operating model transition.
Organisations need to know what they can issue, what they can accept, what assurance sits behind a credential, how a relying party should verify it, what existing processes it can replace, where additional checks are still required, how the experience works for real users, and how the model aligns with AGDIS, IVS, proofing expectations, credential standards, and sector obligations.
This is where early work creates advantage.
A well-designed proof of concept does not just demonstrate that a credential can be issued and verified. It helps an organisation understand the trust decisions around it. It surfaces the legal, risk, security, product, customer, and operational questions that need to be answered before scale.
It also helps distinguish between use cases that are merely interesting and use cases that are structurally valuable.
The most valuable use cases are usually those where digital credentials can reduce repeated proofing, reduce unnecessary data collection, improve confidence, simplify user journeys, or create a more privacy-preserving way to prove eligibility, status, identity, authority, or entitlement.
Waiting for certainty may create the biggest risk
It is reasonable for organisations to want clarity before making major infrastructure decisions.
But there is a difference between waiting for clarity and waiting for completion.
Australia’s framework will continue to mature. Reliance rules will become clearer. Sector expectations will evolve. Credential ecosystems will develop. Wallet adoption will grow unevenly before it becomes normal. Standards and operating practices will continue to settle.
But the direction is now clear enough to begin.
The organisations that start early will build internal fluency. They will understand the difference between AGDIS-based Digital ID, IVS-based verification, mobile credentials, verifiable credentials, wallets, assurance levels, and relying party flows. They will know which use cases are realistic. They will have tested integration patterns. They will have educated internal stakeholders. They will be better positioned to respond when regulation, market demand, or partner expectations accelerate.
Those that wait may find themselves trying to catch up at the point when digital trust is no longer exploratory.
The risk of waiting is not only delayed implementation.
It is lost readiness.
Building while the system forms
Australia has built many of the foundations for a more coherent digital identity future.
The work now is to connect them.
Verification needs to feed reusable trust, not only local decisions. Proofing needs to become a stronger basis for future reuse, not a burden repeated at every boundary. Credentials need to become recognised instruments of reliance, not just technically valid artefacts. AGDIS needs to continue maturing as a governed trust framework while the broader ecosystem develops clearer ways to recognise credentials, assurance, and identity outcomes across sectors.
This will take time. For good reason.
Trust infrastructure should be careful. It should be accountable. It should be inclusive. It should be clear about assurance, liability, privacy, consent, and reliance before it becomes deeply embedded in everyday digital life.
But the fact that the system is still forming does not mean organisations should wait.
Formation is the time to learn.
By the time the framework feels complete, the organisations best positioned to use it will already have done the hard work of understanding how trust moves.